Overview
Client introduction
A FinTech company runs a portfolio of 30+ legacy applications supporting onboarding, payments, and internal operations.
The big picture
The company wasn’t struggling to “move to cloud”, but they were struggling to do it consistently. Every application team had its own deployment style, its own CI pipeline, and its own security steps. So each migration felt like one whole project.
We built a repeatable golden path (templates, CI/CD, environments, security guardrails) backed by GitOps + an Internal Developer Platform (IDP). In simple terms: Teams could self-serve a production-ready baseline in hours, not weeks, while governance stayed consistent across apps. (GitOps keeps the desired state in Git and continuously reconciles runtime to match it. IDPs are built to create “golden paths” and enable developer self-service with lower cognitive load.)
Quick stats (First 90 days after rollout)
- Onboarding time: From 10–15 days → under 1 day (team + pipeline + baseline env)
- Environment provisioning: From 3–5 days → 30–60 minutes (self-service)
- Release frequency: From monthly → weekly for migrated services
- Security drift incidents: Reduced by ~60% via policy-as-code + GitOps reconciliation
Challenges
Primary challenge
The company wanted to migrate multiple legacy apps faster, but their delivery foundation wasn’t repeatable. When one team successfully moved an app, the next team still had to rebuild the same plumbing from scratch: CI/CD pipelines, secrets management, IAM and access policies, environment provisioning, observability (logging/monitoring), approval workflows, and deployment patterns.
Why it mattered (Business context)
Migration timelines had become unpredictable, making it difficult for leadership to plan roadmaps, budgets, and transformation milestones with confidence. Security and audit efforts increased linearly with every additional application, creating operational overhead instead of economies of scale. Developers were spending more time understanding infrastructure, pipelines, and compliance requirements than delivering customer-facing features. As a result, production changes felt inherently risky, release cycles slowed down, and innovation momentum began to stall.
This wasn’t only the business or engineering preference. Without a standardized path, every migration increased operational and compliance risk. The company needed a model where the platform guarantees the baseline standards, and app teams focus on business functionality.
Technical challenges (What made it hard)
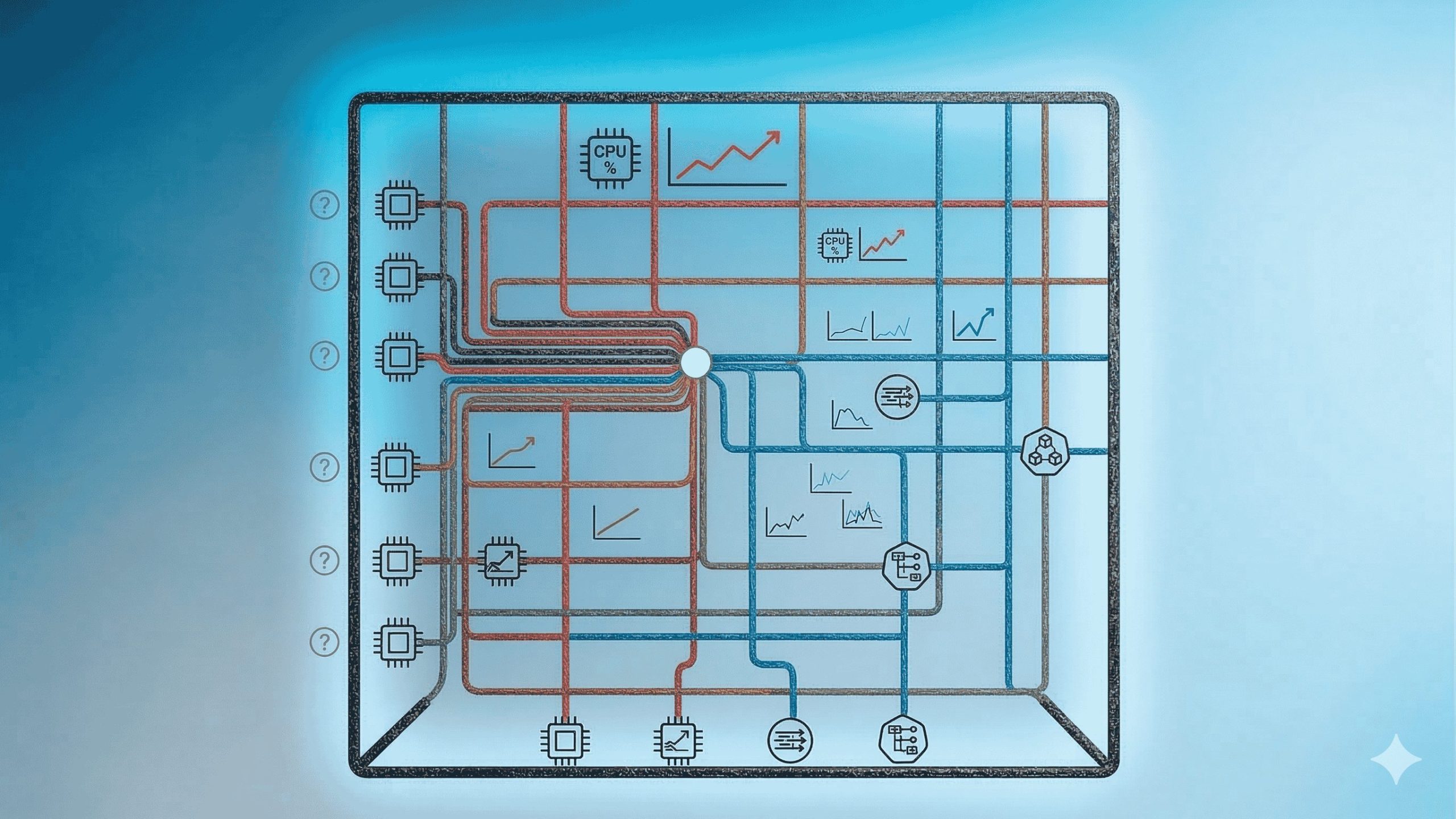
The complexity was increased because of multiple structural gaps across engineering practices. Pipeline sprawl was a major issue because different teams used different CI tools and applied inconsistent quality gates, leading to uneven release standards across repositories. Environment drift further compounded the problem, as development, staging, and production environments were not truly equivalent, causing unexpected failures during deployments.
Security practices also lacked uniformity. Secrets handling, IAM permissions, and network configurations varied from team to team, increasing risk and audit overhead. Adding to this was legacy diversity: the portfolio included VM-based applications, partially containerized services, and tightly coupled monoliths, each requiring a different migration approach. Finally, operational visibility was inconsistent. Logs, metrics, and traces were not standardized, making troubleshooting reactive rather than proactive and increasing mean time to resolution
Strategy
Strategic approach overview
We designed a “migration factory” model: One golden path, many apps. The platform team owns the paved road (templates + automation + guardrails). Application teams consume it through a self-service IDP portal and Git workflows.
How we design a solution architecture using a component-based breakdown
1) Golden Path Templates (The starting line)
We began by creating opinionated, production-ready templates that served as the standardized entry point for all new and migrating services. These templates covered common service types, including API services (REST and gRPC), background workers, scheduled jobs, frontend applications, and a specialized “legacy wrapper” pattern for applications not yet fully modernized.
Each template followed a consistent repository structure, separating infrastructure-as-code (IaC), application code, security and quality checks, and deployment manifests. This ensured clarity, maintainability, and uniformity across teams. Additionally, built-in documentation was included by default, such as operational runbooks, SLO checklists, and incident documentation templates.
2) CI/CD Baseline (Consistent gates, less debate)
To eliminate inconsistencies and reduce repeated discussions around release standards, we introduced a single, reusable pipeline blueprint adopted across teams. This CI/CD baseline embedded mandatory quality and security gates into every service lifecycle. The build stage included unit and integration tests with defined coverage thresholds. Supply chain security was enforced through automated dependency scanning, SBOM generation, and secret detection. Static code analysis and container image scanning ensured code quality and runtime security before deployment.
Promotion rules were standardized across environments. These changes moved from development to staging and production through structured approvals aligned with risk levels. Instead of allowing each team to design its own pipeline, we developed reusable pipeline modules with minimal configuration parameters, such as service name, runtime, and deployment target. This approach preserved flexibility while maintaining governance, ensuring consistency without slowing teams down.
3) Environment Standardization (dev/stage/prod that actually match)
We implemented a structured and consistent environment model to eliminate drift and deployment surprises. Each pull request automatically generated an ephemeral preview environment, enabling fast feedback and testing without relying on unstable shared sandboxes. In parallel, long-lived development, staging, and production environments were standardized with consistent network configurations and identity patterns to ensure parity across stages.
Core baseline services including logging, monitoring, distributed tracing, and a centralized secrets engine were embedded into every environment by default. This architectural consistency removed the long-standing issue of deployments failing due to environmental differences, effectively addressing the classic scenario: “it worked in development but broke in production because production is different.”
4) GitOps Delivery (Continuous reconciliation, no manual drift)
GitOps became the execution backbone of the delivery model. All application deployments and infrastructure changes were defined declaratively and stored in Git as the single source of truth. Instead of manually applying updates to environments, a GitOps controller continuously reconciles the live cluster state to match the desired state defined in the repository.
This approach eliminated configuration drift and reduced reliance on manual interventions. Rollbacks became straightforward and low-risk by reverting a commit automatically triggered the controller to sync the environment back to the previous stable state. Beyond operational stability, this model significantly improved auditability, as every change was captured in Git pull requests with clear visibility into who made the change, what was modified, and why it was approved.
5) Security by default (Guardrails, not speed bumps)
Security was integrated into the golden path so teams don’t “add it later”:
- Identity: OIDC-based auth for CI to cloud (reduce long-lived credentials)
- Policy as Code: Baseline policies enforced at deploy time (e.g., no privileged containers)
- Secrets: Centralized secrets management patterns and rotation hooks
- Network: Standard segmentation patterns + least-privilege service communication
6) Internal Developer Platform (IDP) (Self-service experience)
The Internal Developer Platform (IDP) unified all platform capabilities into a streamlined, developer-friendly interface. Instead of navigating multiple tools and processes, teams interacted through guided workflows. A “Create Service” flow allowed developers to select a pre-approved template, define runtime requirements, and choose target environments. Similarly, a “Create Environment” flow enabled the provisioning of preview environments, development namespaces, or staging resources with standardized configurations.
The platform also introduced a centralized service catalog that captured ownership details, dependencies, runbooks, SLOs, and alert configurations. Additionally, a golden path compliance indicator clearly showed whether a service followed the paved standard route or operated under an approved exception.
Implementation highlights (Key technical decisions)
A critical decision was to treat the platform as a product rather than an internal utility. It had a defined roadmap, measurable adoption metrics, and continuous feedback loops from engineering teams. This ensured the golden path evolved based on real usage patterns instead of remaining a static framework.
We also introduced a “paved road with an exception process” model. While the golden path served as the default and recommended standard, teams could formally request deviations when justified by business or technical needs. This preserved flexibility without diluting governance.
Migration-ready templates were intentionally designed to accommodate legacy realities. Patterns for “legacy wrappers” allowed monolithic or partially modernized applications to integrate into the standardized deployment and observability model without requiring immediate, high-risk refactoring.
Finally, observability was embedded from day one. Logging, metrics, and distributed tracing were included as part of the baseline configuration, ensuring that every service launched with operational visibility built in rather than treated as an afterthought.
Results
Impact summary
Within 90 days, the company shifted from one-off migrations to a repeatable delivery standard that multiple teams could use without platform tickets.
Business impact
The introduction of a standardized golden path significantly improved migration throughput. Three pilot applications were successfully migrated using the same blueprint, proving the model’s repeatability and enabling rapid onboarding of additional teams. Delivery friction was reduced as dependencies between development, operations, and security teams decreased because clear guardrails replaced repetitive coordination. This consistency also enabled more predictable planning, allowing leadership to estimate migration timelines and resource allocation based on a defined, reusable baseline rather than variable team capabilities.
Technical performance outcomes
From a technical standpoint, deployment confidence increased substantially. Standardized environments reduced unexpected production failures caused by drift or misconfiguration. Change velocity improved as well and weekly releases became achievable and sustainable for services built on the golden path. The organization’s security posture strengthened through embedded policy enforcement, resulting in fewer violations and reduced need for emergency production fixes. Additionally, platform stability improved as logging and alerting were standardized, shortening the time required to detect and diagnose incidents.
What changed (before vs after)
Before the solution, every team built and managed CI/CD pipelines in its own way, leading to inconsistency and duplicated effort. Environments gradually drifted apart due to manual changes and lack of standardization, increasing deployment risk. Security reviews repeatedly covered the same baseline questions because there was no embedded guardrail model. Ultimately, migration speed depended heavily on which team had the strongest DevOps expertise rather than on a repeatable system.
After implementing the golden path, common service types followed a standardized blueprint that teams could adopt immediately. Environments became self-service yet consistent, with predefined baselines that reduced drift. All changes were managed through Git-based workflows, making them auditable, transparent, and reviewable. Most importantly, platform guardrails were embedded directly into daily workflows, allowing teams to move faster without compromising security or governance.
Stakeholder feedback (client voice)
“Earlier, every migration felt like a new project with new risks. Now we have a path that teams trust, and it’s fast enough that migration is no longer a blocker.” — Head of Engineering
FAQs
What exactly is the “golden path” in this case study?
It’s a set of standard templates + pipelines + environment patterns + security defaults that teams reuse. The goal is not to restrict teams, but it’s to make the “safe default” the easiest option. Teams can still deviate, but deviations become a conscious decision with an approval trail.
Why GitOps instead of only CI/CD pipelines?
CI/CD pushes changes, but GitOps adds continuous reconciliation. That means if something drifts (manual change, config mismatch), the system corrects back to the declared state in Git. This reduces drift-based incidents and improves auditability.
What technologies can power this setup?
This setup can be implemented using a range of proven cloud-native and DevOps technologies. A GitOps controller such as Argo CD or Flux manages declarative deployments, typically running on Kubernetes or a managed Kubernetes service. Infrastructure provisioning is handled through Infrastructure-as-Code tools like Terraform or Crossplane, while secrets management is centralized using Vault or cloud-native secret managers. Policy enforcement is implemented using policy-as-code solutions such as OPA or Gatekeeper, ensuring compliance is validated automatically during deployment. CI pipelines are standardized using platforms like GitHub Actions, GitLab CI, or Jenkins.
The specific tooling may vary by organization, but the core principle remains the same: declarative infrastructure, automated policy enforcement, secure identity management, and consistent CI/CD workflows.
How did you handle apps that weren’t container-ready?
For applications that were not immediately container-ready, we adopted a staged modernization approach. In the first phase, we wrapped legacy applications with a standardized deployment layer that introduced consistent CI pipelines, release processes, logging, and observability without requiring a full rewrite. This allowed teams to benefit from the golden path immediately while reducing operational risk.
In the second phase, we applied incremental modernization techniques, such as the strangler pattern, gradually decomposing monolithic components into smaller services where appropriate. This ensured modernization was practical and business-aligned, rather than forcing disruptive, high-risk rewrites.
How does this scale across multiple teams and clouds?
The design scales because the interface stays the same: teams interact via templates + Git workflows + the IDP portal. Cloud-specific differences are abstracted into standardized modules (network, IAM, clusters, logging) so teams don’t reinvent per cloud. This is also where the IDP becomes a maturity marker: self-service with consistent standards.
What’s the biggest lesson learned?
Golden paths succeed when they are:
- Fast (clearly faster than the DIY route)
- Trusted (security + reliability built-in)
- Owned (platform team treats it like a product with feedback loops)